A few years ago I wrote about using Thawte’s personal e-mail signing certificates for setting up secure S/MIME encryption with Apple Mail. Well, Thawte, so I understand, is phasing out that service. So, I’ve been wondering how to do self-signing on the Mac to set up S/MIME encrypted e-mails. This evening, I found out.
Credit where it is due: James Walker’s post on how to set up self-signed certificates for e-mail with OS 10.4. His post gave me a few steps to follow that I’m just updating here to match what is needed for Mac OS 10.6.
Create your certificate
Open up Keychain Access. This is an application in your Applications/Utilities directory. (It is faster to just hit command+spacebar to open Spotlight, then enter keych, and hit the enter key when Keychain Access appears highlighted.)
Click on the Keychain Access menu, hover over the Certificate Assistant option, and then select Create a Certificate….
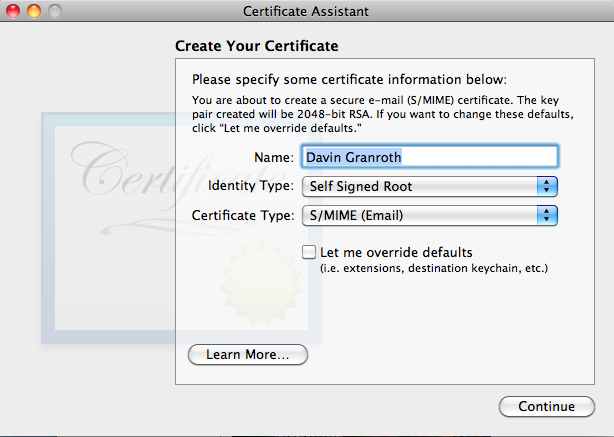
Here are a few details to note about the Create Your Certificate options.
- You might want to add an e-mail descriptor to the name field. E.g., Davin Granroth (gmail).
- Go with Self-Signed Root and S/MIME (Email).
- By default, the certificate will be valid for a year. If you want to extend that a bit, you need to check the Let me override defaults checkbox. You’ll get to make changes after you click the Continue button.
- If you need a certificate for your non-primary e-mail account, you’ll need to check the Let me override defaults box for that too.
If you checked the override box, you’ll eventually see a series of Extension windows. Just go with the default values. Apple figures out what you need based on the first screen where you chose the certificate type.
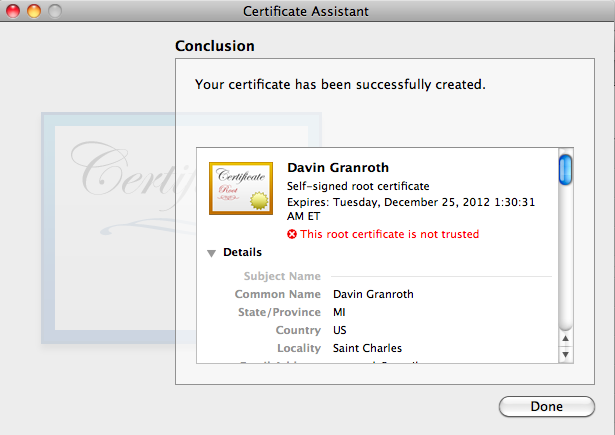
Continue and you’ll see a window with your new certificate information in it. Congratulations!
Now if you could only trust that certificate.
Trusting your certificate
If you haven’t already, click the Done button to close that Certificate Assistant window. Now, back in Keychain Access, click on the My Certificates category on the right of the main Keychain Access window.
You’ll see your new certificate listed with a little white X in a red circle on the icon. That indicates the certificate is not trusted. Double-click on the certificate, and a new window will open with details of the certificate.
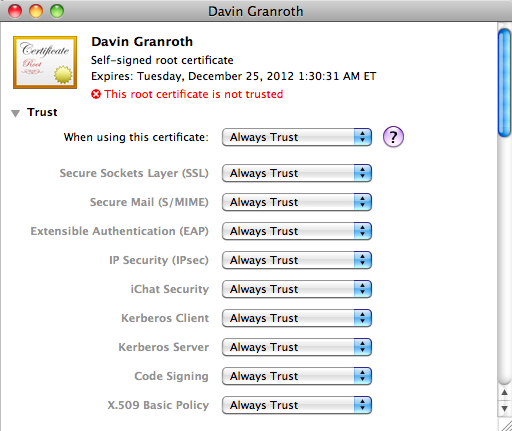
Near the top of that window you’ll notice the word Trust with a little triangle to the left of it. Click the triangle to twist open the Trust options.
In the When using this certificate select list, select Always Trust. Then close that window. You’ll be prompted for your administrator password. Enter it, and you should be all set. Your new certificate should now be trusted.
Sending signed or encrypted e-mails
At this point, if you restart Apple Mail, you’ll notice a new option available when you compose a message.
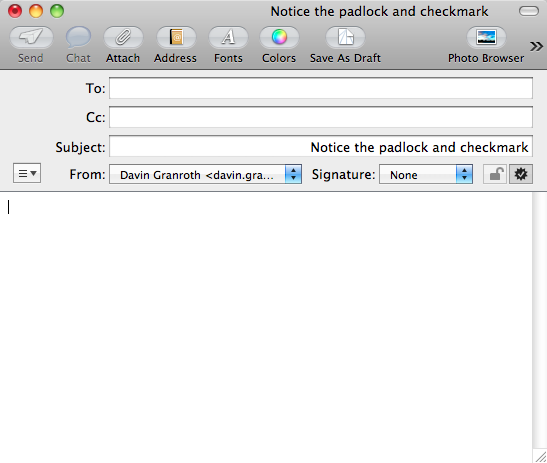
For more on exchanging signed or encrypted e-mails, see James Walker’s article. Scroll down to the section on Exchanging Signed or Encrypted E-mail.
Why would you want to send encrypted e-mails?
Hah! “Why wouldn’t you want to,” is the better question. Actually, if you send or receive sensitive information like usernames and passwords, legal information, or confidential business information, you might really want to consider this.
The trick is getting the person you exchange these messages with to also set up S/MIME on their end of the e-mail.

8 responses to “Signing and Encrypting E-mail on Mac OS X 10.6 Using Self-Signed Certificates”
Hi,
I’ve installed a certificate from http://www.comodo.com and added it to my keychain.
So far I can only sign email but the encryption icon remains inactive.
Why can’t I encrypt my e-mails?
Please help!
Hi Peter, to send an encrypted message, you need to first send a signed message to the person with whom you want to exchange encrypted messages. That person needs to mark your certificate as trusted. Then that person needs to send his or her signed message to you for you to trust. Once you’ve each done that, you can exchange encrypted messages with each other.
For a slightly more detailed workflow, scroll down on this page to the section on exchanging signed/encrypted messages: http://jwwalker.com/pages/certificates.html
Good luck.
the description of how to make your own certificate as written above is awesome. Works well.
So why would anyone (personal/small business) need/want to get one from Verisign or Comodo? Is there an advantage?
Hi Mike, thanks for the comment.
If a person were to get a certificate from an authority like Verisign, the benefit (I think) is that it will already be marked as trusted. So, the sender and recipient won’t need to take that extra step of manually marking the certs as trusted. Not that much of a benefit perhaps, but depending on the situation it might be worth it.
So, James Walker’s article mentions Apple Mail and Thunderbird. Presumably the person receiving the email needs to use one of those two?
Sorry, but I did not see contact info on his website.
Hi Matt, the recipient needs to use an e-mail client that can handle S/MIME. There are plenty of them. This article talks a little more about S/MIME from a Windows user’s perspective, and it lists a few other e-mail programs, including Outlook:
http://www.marknoble.com/tutorial/smime/smime.aspx
Hi Davin!
I have the new option available when I compose a message, but it’s grayed out. I wonder why?
Thanks!
Hi Denis, unless I’m mistaken, you should have an option to sign the message, which shouldn’t be greyed out, and the option to encrypt the message will be greyed out except for recipients whose public keys you have on your system. They would need to send you a signed message so you have their public key.